It’s 2024, and the internet has become an integral part of our lives. Despite our perceptions of being protected, the reality remains that we are almost as vulnerable as we were at the outset. According to IBM, the average cost of a data breach reached $4.45 million in 2023, marking the highest average on record. Verizon also highlights that 74 percent of cybersecurity breaches are due to human error. So, what steps can be taken to ensure safety?
We aim to share our knowledge and insights to guide your team in establishing a robust, proactive cybersecurity strategy. Here’s what you need to know to navigate the complexities of protecting your organization effectively.
A Proactive approach involves taking proactive measures to prevent attacks before they happen. The goal of this type of security is to identify potential vulnerabilities in your network long before they can be exploited. Examples of preventative cybersecurity measures include the use of firewalls and threat detection. It also includes regular analysis of vulnerabilities and training employees on proper cyber hygiene.
On the other hand, Reactive cybersecurity involves tasks such as patch management, log monitoring, and SIEM. These are primarily focused on remediating the current incident and preventing future attacks or technology failures from recurring.
The reactive approach can only protect against known threats, and it’s not a sufficient way to safeguard your organization against unknown possibilities. With the growing amount of modern advanced cyber assault vectors, it’s time to think about how you can protect your business.
But is one approach fundamentally better than the other?
What is reactive security?
Reactive security practices are considered an important product of a cybersecurity strategy.
A Reactive strategy aims to strengthen your defenses against common attack vectors and cyber risks, as well as detect whether attackers have penetrated your defenses and network.
Responsive cybersecurity strategies are utilized to guard against more conventional assaults. Basically, they include looking for self-evident signs of interruption and indicators of compromise (IoC), and only after that, taking action.
And it makes sense: when it comes to basic assaults, the time it takes for an assailant to do harm surpasses the time it takes to identify and react to an occurrence.
General reactive security measures include:
- Firewalls
- Antivirus solutions
- Spam filters
- Disaster recovery plans
- Vulnerability assessments
How reactive security works in practice
Antivirus solutions, endpoint detection, and response systems are basic tools that almost everyone knows. But the most important thing to prioritize is a disaster recovery plan. We’ll talk about it a bit more below.
Let’s take a high-level look at how the most popular and effective reactive security practices can help protect your business.
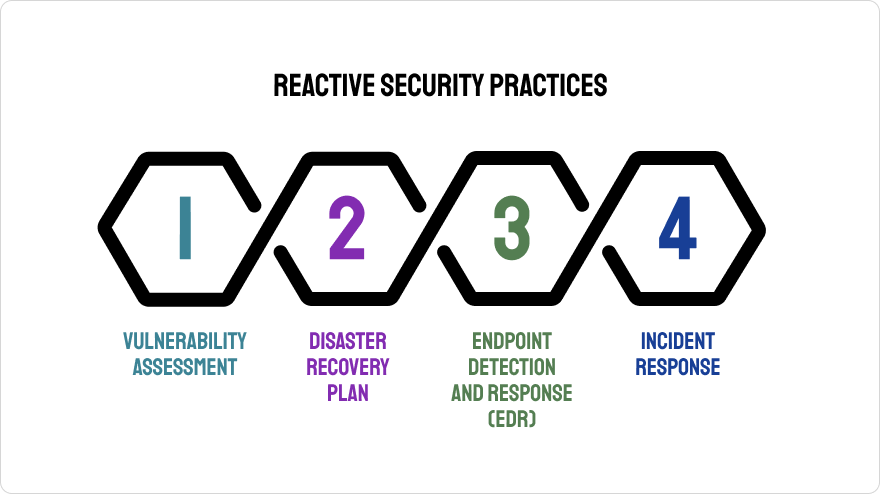
- A vulnerability assessment, also known as a vulnerability analysis, is a systematic process of identifying, assessing, prioritizing and proposing solutions to eliminate or mitigate vulnerabilities in a network or system. Simply put, it is a review of security vulnerabilities in an organization’s information systems.
- As the name implies, a disaster recovery plan is the steps a company should take after a cyberattack. It includes all the policies, tools and procedures that will help your organization recover from attacks, data breaches and even natural disasters such as floods.
- Endpoint detection and response (EDR) solutions help organizations detect threats in their IT environments and investigate their lifecycle. This helps you understand how threats bypass existing defenses, how they behave when they enter your network, and provides insight into how to categorize and mitigate threats.
- Incident response (IR) is an approach that includes policies and procedures for responding to and managing cyberattacks and their consequences. If a security incident is not properly handled and contained, it can escalate into a more serious problem leading to a large-scale data breach, resulting in financial loss and business interruption.
What’s the problem?
Although at first glance it appears that reactive security is completely self-sufficient, this doesn’t tell the whole story. Often, the biggest problem is that organizations or businesses rely solely on reactive measures to provide adequate protection and cyber resilience, when it should really be part of the larger data protection strategy.
What is proactive security?
Proactive security encompasses the techniques used to prevent cyberattacks. While reactive security primarily focuses on detecting threats when they become aggressive and infiltrate your network, proactive security attempts to detect and address an organization’s vulnerabilities before they are exploited by cybercriminals.
A proactive security approach can help organizations prevent serious security incidents and data breaches before they happen. These measures are taken to anticipate possible scenarios and prevent data theft, data breaches and cyber extortion, as well as financial, reputational and operational losses.
Popular preventative cybersecurity practices include:
- Ethical hacking
- Pentesting
- Data Loss Prevention (DLP)
- Attack surface management
- Organizational cybersecurity awareness
Best practices in proactive security
A proactive approach to security and proven best practices can help you detect threats and vulnerabilities before they are exploited.
This can prevent incidents from occurring, saving you time and the stress of waiting for something to happen so you can respond.
What are the main types of protection:
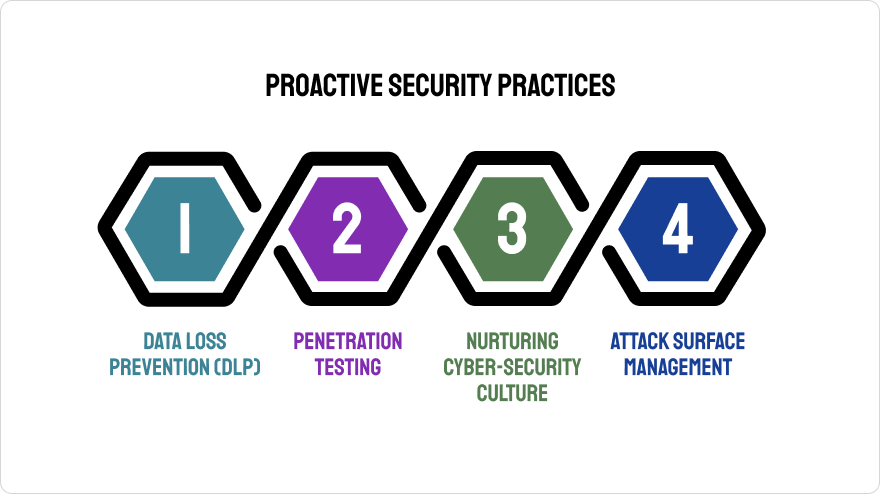
- Data loss prevention (DLP) is a set of processes, procedures, and tools designed to prevent data loss by preventing unauthorized users from accessing an organization’s data. This is done to protect sensitive data from unauthorized users and prevent misuse by authorized users.
- Penetration testing (commonly known as pentest) is the act of an ethical hacker testing a system, network, or application to find security vulnerabilities that can be exploited by an attacker.
- Fostering a culture of cybersecurity. There are some obvious steps you can take to promote a safety culture within your company: For example, train employees not to click on suspicious links, not to divulge passwords, and not to use different passwords.
- Attack surface management is an important proactive cybersecurity approach that involves the continuous identification, inventory, classification, monitoring, and prioritization of all of an organization’s digital assets, representing the organization’s attack surface. This allows organizations to identify all attack target components, attack vectors, and network impacts, and use this knowledge to proactively defend against future attacks.
What is the real issue?
Oddly enough, the problem is on the plane of choice. Organizations are more likely to rely on reactive defenses and deal with the problem as it comes, since some deem the cost of proactive protection costly and unnecessary. Guided by the logic of “we’ll solve it when we need to”, companies often find themselves in situations where they have to resort to extreme measures and act as quickly as possible, which only increases the resulting costs.
So what’s best and what to choose?
As you’ve now had an overview of Reactive and Proactive security measures, the question is: Which is best for your organization?
It turns out, the answer is both!
While it’s critical to understand the differences between reactive and proactive security, and to know their values in cybersecurity, one isn’t superior to the other. A comprehensive cybersecurity approach requires the use of both.
It’s critical to take a holistic view and to see security breaches and other incidents as something that will happen, not something which could happen.
By preparing for dangers and reacting fittingly to these occurrences, you can ensure better cybersecurity situations for your business.
Ready to take the next step? Let’s discuss your project.